Introduction
This guide will help you use the Shodan API through Tines to automate security monitoring and threat intelligence workflows. Tines is a no-code security automation platform that lets you connect Shodan with your existing security stack to build powerful, event-driven workflows — no plugins or custom code required.
Prerequisites
- Tines Account: You'll need access to a Tines tenant. A free Community Edition is available.
- Shodan API Key: You'll need a Shodan API key. You can get one by signing up on the Shodan website. A free tier is available, but paid plans offer more credits and capabilities.
Setup Credentials
Tines uses Credentials to securely store API keys and reuse them across stories.
- In Tines, navigate to Credentials in the left sidebar.
- Click New Credential and select New.
- Search for Shodan — a window will appear prompting you to enter your Shodan API key.
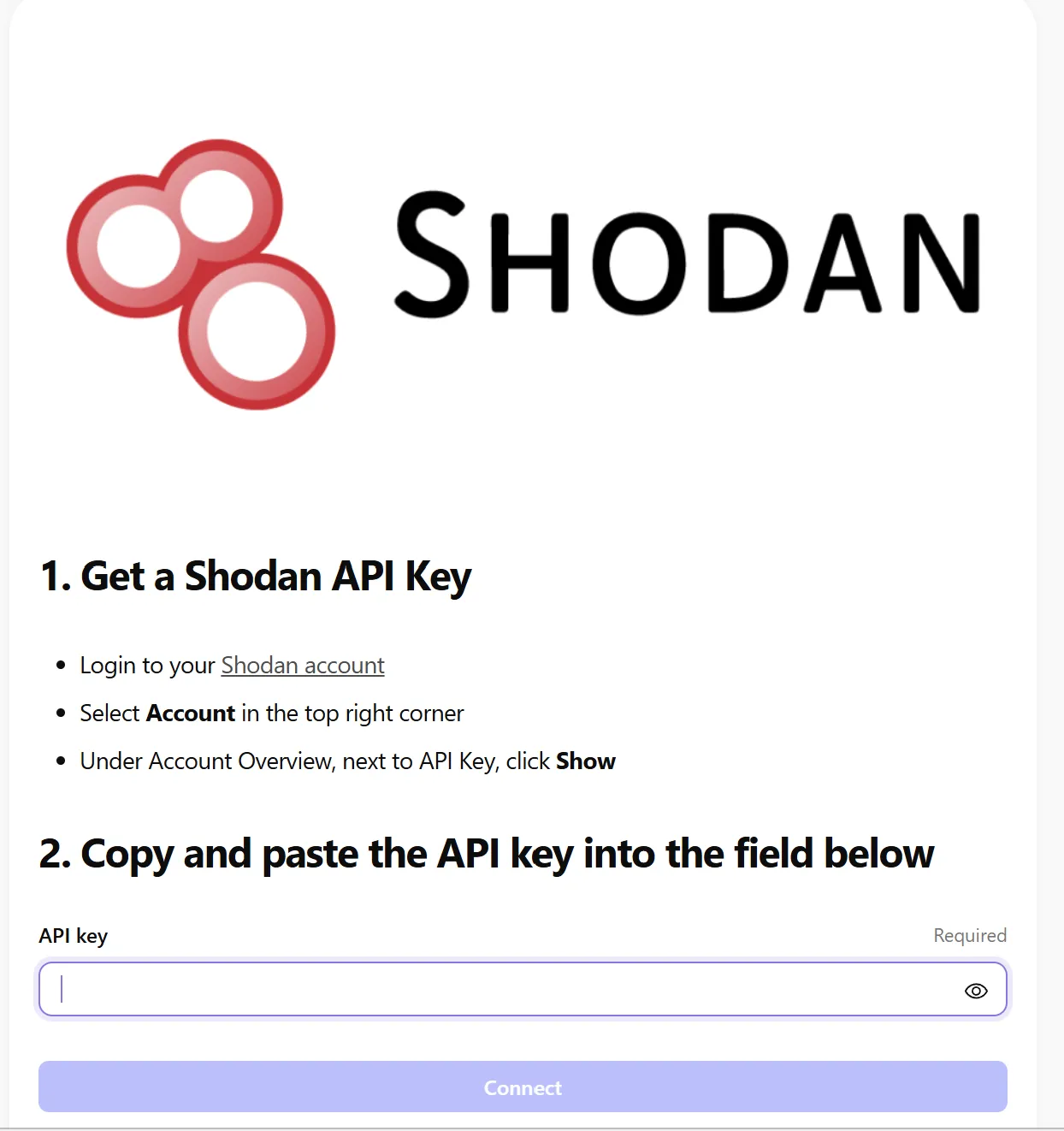
You can now reference this credential in any HTTP Request action as CREDENTIAL.shodan.
Shodan Templates in Tines
Tines provides 27 ready-made Shodan templates to help you get started quickly without building stories from scratch.
How to access them
- In the Tines canvas, click Templates in the left sidebar.
- In the search bar, type Shodan.
- Select Shodan — 27 templates from the results.
- Browse and click any template to import it directly into your story.
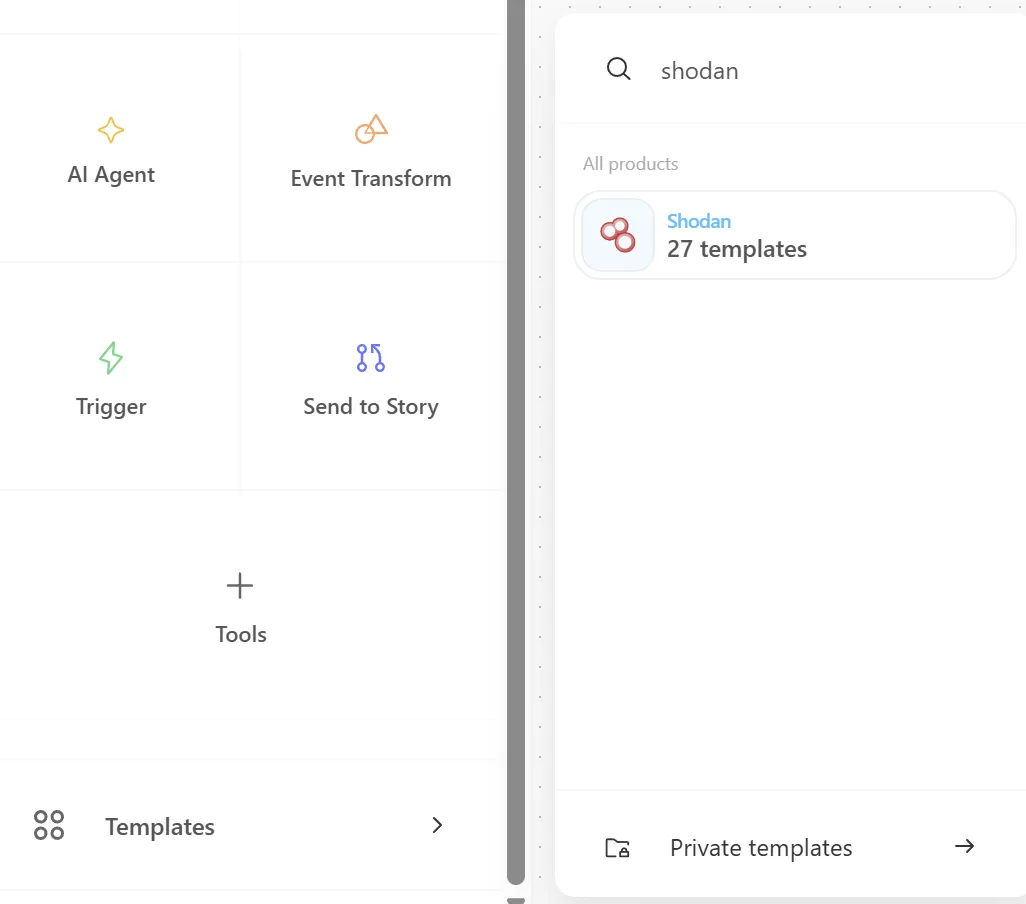
What's included
The templates cover a wide range of common Shodan workflows, including host lookups, vulnerability searches, DNS reconnaissance, asset discovery, and more — all pre-configured and ready to customize with your own API key.
Examples
1. Monitor Your Infrastructure
Automatically scan your IP ranges for newly exposed services and alert your team.
Story structure:
- Add a Scheduled Trigger (e.g., runs daily at 08:00 UTC).
- Select the Shodan template Search Shodan using query with parameters:
key→CREDENTIAL.shodanquery→net:203.0.113.0/24
- Add an Event Transform action to extract relevant fields (IPs, ports, product names).
- Add a Send Email or Post to Slack action to deliver the alert to your team.
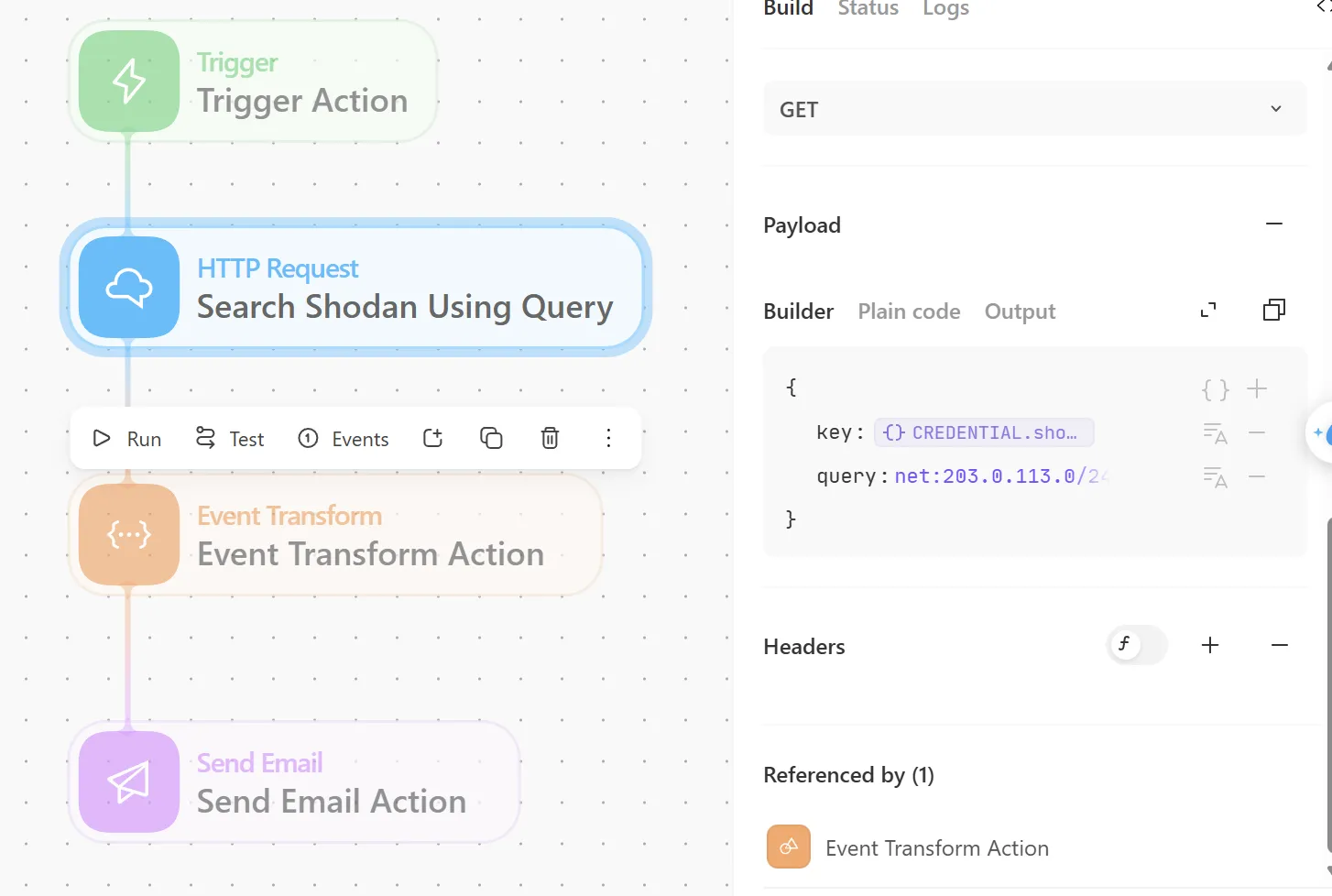
2. Vulnerability Assessment
Trigger a search for hosts in your org that match a known CVE, and export the results as a CSV delivered to your email.
Story structure:
- Add a Manual Trigger or connect to a Webhook from your vulnerability feed.
- Select the Shodan template Search Shodan using query with parameters:
key→CREDENTIAL.shodanquery→org:"Google" vuln:CVE-2021-44228
- Add an Event Transform action in Message only mode to convert the results into a CSV:
OBJECTS_TO_CSV(search_shodan_using_query.body.matches)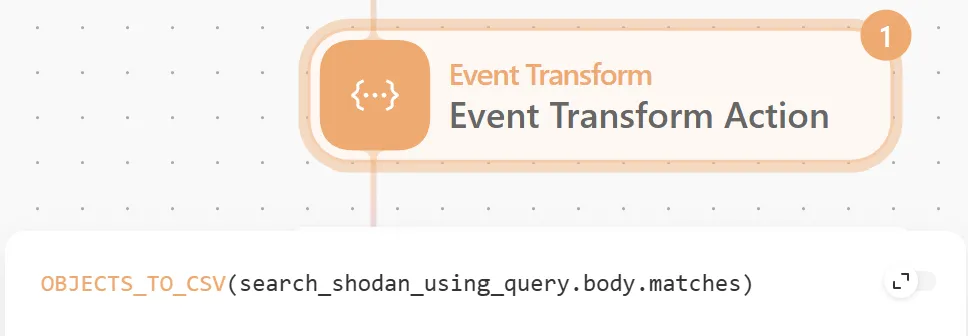
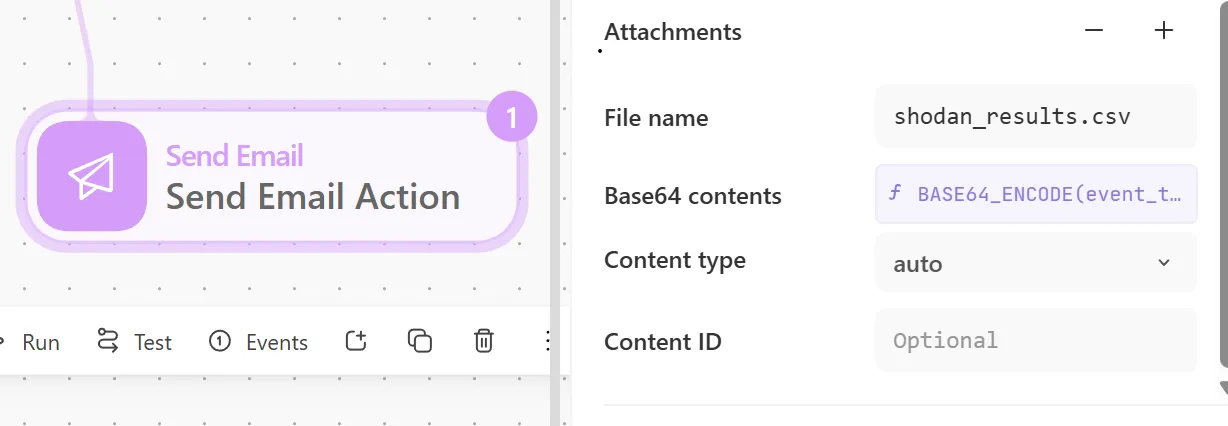
- Add a Send Email action and expand the Attachments section:
- File name →
shodan_results.csv - Base64 contents →
BASE64_ENCODE(event_transform_action.body.csv_output)
- File name →